After releasing its Global Threats research in 2022, Blackberry has recently highlighted the main threats it sees affecting businesses in Australia and New Zealand in 2023.
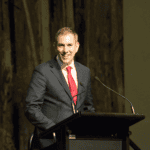
Jonathan Jackson, APJ director of engineering for BlackBerry, said cyber criminals would take advantage of outdated security architectures, the human skills gap and software supply chain vulnerabilities.
“Organisations undergoing digital transformation, particularly in healthcare, will be the most at risk unless they can combine cyber security upskilling and outsourcing with behavioural analytics and AI to improve visibility, prevention, and response to cyber threats in 2023 and beyond,” he said.
The five top cyber attacks that BlackBerry has predicted for 2023 predictions evasion tactics that will evolve as cyber and ransomware attacks spike; increased attacks on healthcare organisations and hospitals, a widening in the cyber security skills gap, quantum computing and supply chain attacks.
Mr Jackson said cyber criminals would be relentless in carrying out more sophisticated and targeted attacks in the year ahead.
“To maximise harm to government and society, and cause more financial impact on the private sector, new tactics, techniques, and procedures (TTPs) will evolve to try and stay one step ahead of vendors, ‘tricking’ both humans and technology,” he said.
He said organisations should prepare for the coming year by looking at their software stack as evasion tactics are on the rise.
“HEAT attacks (highly evasive adaptive threats) can even turn cyber security technology on itself with clever bypass techniques. One recent example tricked certain software into purposely wiping data, instead of protecting it,” he said.
“The use of tactics such as Whispergate and Hermetic Wiper escalated during the Ukraine war, and we will see further impact to businesses in 2023.”
Ransomware attacks will also continue to be one of the biggest risks to companies, especially those using profitable double extortion tactics. Not only does this result in financial loss due to the ransom, but also reputational damage and other direct and indirect losses related to the breach.
Business email compromise (BEC) is another explosive threat.
By exploiting “inbox trust”, cyber criminals can hack, spoof or impersonate a business email address that appears to be genuine.
“In Australia, one of the countless examples in 2022 included tricking home buyers with fake real estate emails,” he said.
“In some cases, people lost their home deposit during settlement, prompting warnings from the government. In 2023, businesses will need to consider more defined risk mitigation strategies, combining employee education with technology tools to stop BEC attacks at multiple levels, including human error, data and network layers.”
BlackBerry research reveals those surveyed in the healthcare sector are least likely to agree they have an incident management process to handle threats.
Over a third said they lack the security teams and tools to be effective, half said they have the capacity to handle the number of alerts they receive, and less than half said they have the knowledge, tools, and necessary visibility to detect and respond to zero-day and advanced threats.
Mr Jackson said quantum computing (QC) would challenge cryptography, fundamentally changing the way in which data is kept secure.
“When quantum computers develop to the point they can break widely used public encryption keys — it could allow access to transportation systems, hospitals, critical infrastructure — even banks,” he said.
“The implications for Y2Q are drawing alarmingly close, with predictions ranging from 2024 to 2032. If Australia is to be ‘the most cyber-secure country in the world by 2030’, as quoted recently by Minister for Home Affairs and Cyber Security Claire O’Neil, the challenge of a quantum-resistant nation should be at the top of the priority list for government and industry in terms of regulatory frameworks, future-proofing embedded systems and the supply chain.
“To achieve this, firming up collaboration between the public and private sector is critical in 2023, at home and internationally.”
Software supply chain attacks are among the most destructive strategies used by cyber criminals.
New BlackBerry research found that four in five IT decision-makers have been notified of an attack or vulnerability in their supply chain in the last 12 months. It also revealed in the last year that 80 per cent of companies in Australia were notified of a vulnerability or attack within their software supply chain.
Compared to the global average, Australia suffered the highest rates of operational compromise and data loss.
“To best prepare for 2023, organisations should consider meaningful and timely contextual threat intelligence to stay up to date with the most recent threat models,” Mr Jackson said.
“It is also important to prioritise defensible security architectures based on zero-trust strategies and establish regular audit programs to identify potential vulnerabilities and weak points in supply chain processes and systems.”