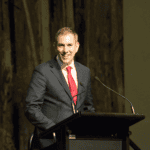
According to Anthony Ferrante, Global Head of Cyber Security at FTI Consulting, third parties can become access points for cyber actors.
“The third-party supplier may assume that the organisation that hired it is properly protected, and therefore, it is secure as well,” Mr Ferrante said. “Meanwhile, third-party suppliers have vendors of their own, and it is possible that these ‘fourth-party suppliers’ are in fact inadvertently granted access to the sensitive data of the original hiring organisation.”
Read more at Business Australia